VRM Day is today, 24 October, at the Computer History Museum. IIW follows, over the next three days at the same place. (The original version of this post was October 17.)
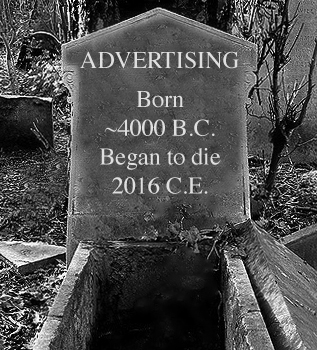
We’ve been doing VRM Days since (let’s see…) this one in 2013, and VRM events since this one in 2007. Coming on our tenth anniversary, this is our last in Phase One.
 The
The difference between Phase One and Phase Two is that between rocks and snowballs. In Phase One we played Sisyphus, pushing a rock uphill. In Phase Two we roll snowballs downhill.
difference between Phase One and Phase Two is that between rocks and snowballs. In Phase One we played Sisyphus, pushing a rock uphill. In Phase Two we roll snowballs downhill.
Phase One was about getting us to the point where VRM was accepted by many as a thing bound to happen. This has taken ten years, but we are there.
Phase Two is about making it happen, by betting our energies on ideas and work that starts rolling downhill and gaining size and momentum.
Some of that work is already rolling. Some is poised to start. Both kinds will be on the table at VRM Day. Here are ones currently on the agenda:
- VRM + CRM via JLINC. See At last: a protocol to link VRM and CRM. , and The new frontier for CRM is CDL: customer driven leads. This is a one form of intentcasting that should be enormously appealing to CRM companies and their B2B corporate customers. Speaking of which, we also have—
- Big companies welcoming VRM. Leading this is Fing, a French think tank that brings together many of the country’s largest companies, both to welcome VRM and to research (e.g. through Mesinfos) how the future might play out. Sarah Medjek of Fing will present that work, and lead discussion of where it will head next. We will also get a chance to participate in that research by providing her with our own use cases for VRM. (We’ll take out a few minutes to each fill out an online form.)
- Terms individuals assert in dealings with companies. These are required for countless purposes. Mary Hodder will lead discussion of terms currently being developed at Customer Commons and the CISWG / Kantara User Submitted Terms working group (Consent and Information Sharing Working Group). Among other things, this leads to—
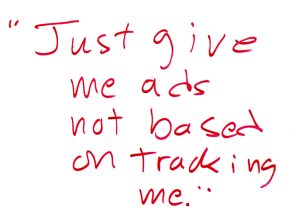 Next steps in tracking protection and ad blocking. At the last VRM Day and IIW, we discussed CHEDDAR on the server side and #NoStalking on the individual’s side. There are now huge opportunities with both, especially if we can normalize #NoStalking terms for all tracking protection and ad blocking tools. To prep for this, see Why #NoStalking is a good deal for publishers, where you’ll find the image on the right, copied from the whiteboard on VRM Day.
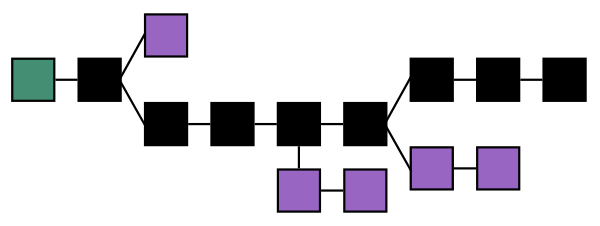
Next steps in tracking protection and ad blocking. At the last VRM Day and IIW, we discussed CHEDDAR on the server side and #NoStalking on the individual’s side. There are now huge opportunities with both, especially if we can normalize #NoStalking terms for all tracking protection and ad blocking tools. To prep for this, see Why #NoStalking is a good deal for publishers, where you’ll find the image on the right, copied from the whiteboard on VRM Day.- Blockchain, Identity and VRM. Read what Phil Windley has been writing lately distributed ledgers (e.g. blockchain) and what they bring to the identity discussions that have been happening for 22 IIWs, so far. There are many relevancies to VRM.
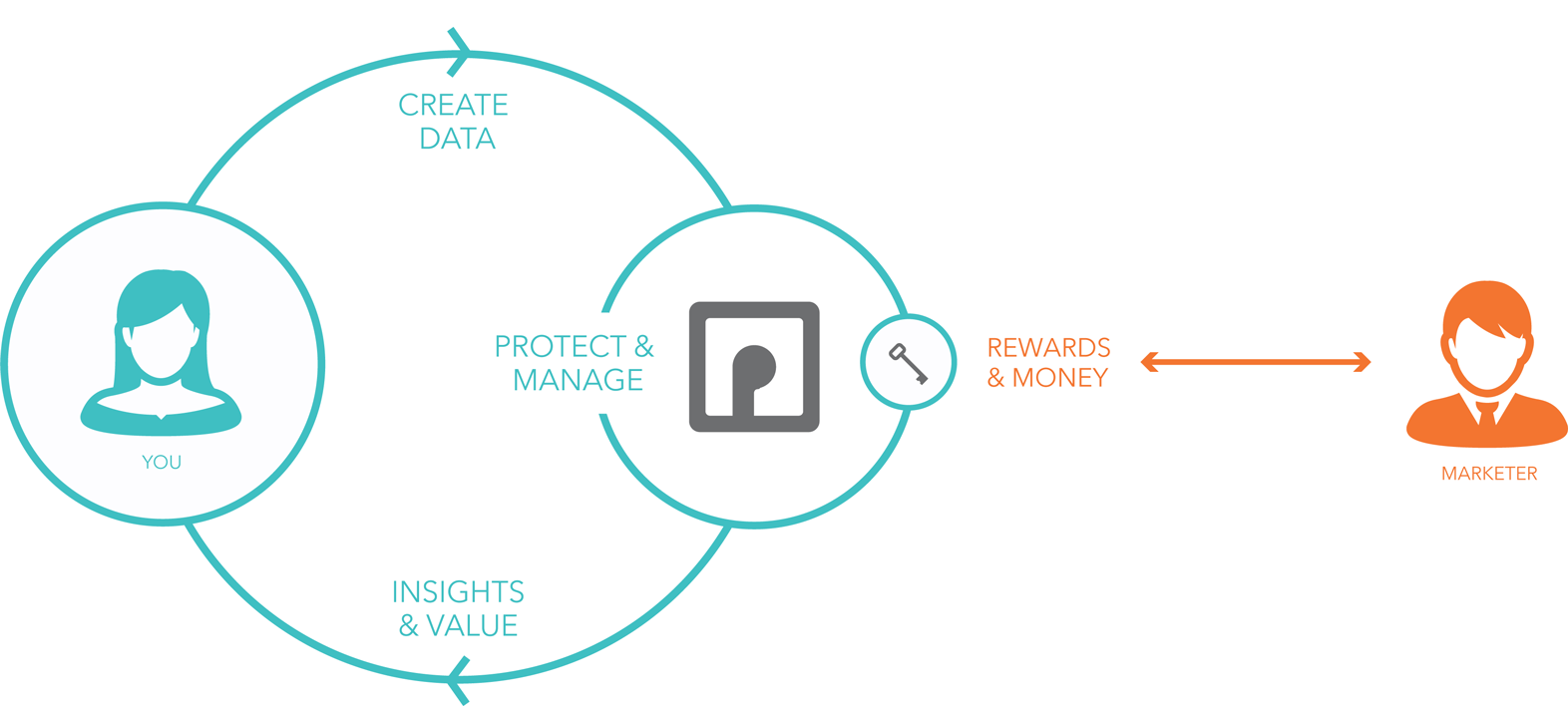
- Personal data. This was the main topic at two recent big events in Europe: MyData2016 in Helsinki and PIE (peronal information economy) 2016 in London. The long-standing anchor for discussions and work on the topic at VRM Day and IIW is PDEC (Personal Data Ecosystem Consortium). Dean Landsman of PDEC will keep that conversational ball rolling. Adrian Gropper will also brief us on recent developments around personal health data as well.
- Hacks on the financial system. Kevin Cox can’t make it, but wants me to share what he would have presented. Three links: 1) a one minute video that shows why the financial system is so expensive, 2) part of a blog post respecting his local Water Authority and newly elected government., and 3) an explanation of the idea of how we can build low-cost systems of interacting agents. He adds, “Note the progression from location, to address, to identity, to money, to housing. They are all ‘the same’.” We will also look at how small business and individuals have more in common than either do with big business. With a hint toward that, see what Xero (the very hot small business accounting software company) says here.
- What ProjectVRM becomes. We’ve been a Berkman-Klein Center project from the start. We’ve already spun off Customer Commons. Inevitably, ProjectVRM will itself be spun off, or evolve in some TBD way. We need to co-think and co-plan how that will go. It will certainly live on in the DNA of VRM and VRooMy work of many kinds. How and where it lives on organizationally is an open question we’ll need to answer.
Here is a straw man context for all of those and more.
- Top Level: Tools for people. These are ones which, in legal terms, give individuals power as first parties. In mathematical terms, they make us independent variables, rather than dependent ones. Our focus from the start has been independence and engagement.
- VRM in the literal sense: whatever engages companies’ CRM or equivalent systems.
- Intentcasting.
- PIMS—Personal Information Management Systems. Goes by many names: personal clouds, personal data stores, life management platforms and so on. Ctrl-Shift has done a good job of branding PIMS, however. We should all just go with that.
- Privacy tools. Such as those provided by tracking protection (and tracking-protective ad blocking).
- Legal tools. Such as the terms Customer Commons and the CISWG are working on.
- UI elements. Such as the r-button.
- Transaction & payment systems. Such as EmanciPay.
Those overlap to some degree. For example, a PIMS app and data store can do all that stuff. But we do need to pull the concerns and categories apart as much as we can, just so we can talk about them.
Kaliya will facilitate VRM Day. She and I are still working on the agenda. Let us know what you’d like to add to the list above, and we’ll do what we can. (At IIW, you’ll do it, because it’s an unconference. That’s where all the topics are provided by participants.)
Again, register here. And see you there.
Save
Save
Save
Save




 I’m serious.
I’m serious.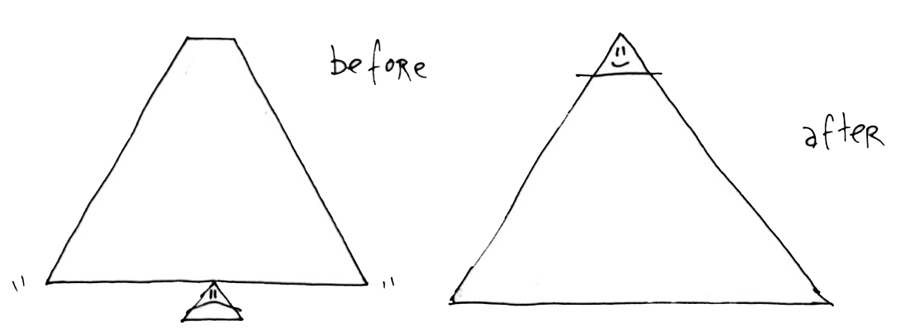

 In
In